Cybersecurity Concerns on UAV Operations: Safeguarding the Skies
Unmanned Aerial Vehicles (UAVs), popularly known as drones, have become an integral part of various industries, revolutionizing fields such as agriculture, construction, aerial photography, and package delivery. However, as the use of UAVs expands, so do the cybersecurity concerns associated with their operations. Ensuring the safety and security of these autonomous flying machines is crucial to prevent potential cyber threats and protect the privacy of individuals and organizations. In this article, we will explore the key cybersecurity concerns related to UAV operations and discuss effective measures to safeguard these airborne systems.
Vulnerabilities in UAV Communication Systems:
One of the primary cybersecurity concerns in UAV operations is the vulnerability of their communication systems. UAVs rely on wireless communication networks to transmit data between the aircraft and the ground control station. However, these communication links can be targeted by malicious actors who may attempt to intercept or manipulate the data being transmitted. To mitigate this risk, encryption techniques and secure communication protocols must be implemented to ensure the confidentiality and integrity of the data exchanged. Reference: [1]

Unauthorized Access and Control:
Another significant concern is the potential for unauthorized access and control of UAVs. As drones often operate over public airspace, they are susceptible to being hacked or hijacked by cybercriminals. Once compromised, these rogue actors can gain control over the UAV, leading to potentially dangerous situations. Implementing strong authentication mechanisms, such as multi-factor authentication, and adopting secure access control protocols can help prevent unauthorized access and maintain control over UAV operations. References: [2], [3]
Malware and Software Vulnerabilities:
UAVs are equipped with sophisticated software systems that control their flight, navigation, and data processing. However, these software systems can be vulnerable to malware attacks and software vulnerabilities. Cyber attackers can exploit these weaknesses to manipulate the UAV’s behavior, compromise its sensors, or even cause a complete system failure. Regular software updates, rigorous code review processes, and the use of trusted software sources are essential to address these concerns and ensure the integrity of UAV operations. References: [4], [5]
Data Privacy and Confidentiality:
UAVs capture and transmit a vast amount of data, including aerial imagery, sensor readings, and telemetry data. Protecting the privacy and confidentiality of this data is crucial, as it may contain sensitive information about individuals or organizations. Secure data storage, encryption during transmission, and strict data access controls are fundamental to safeguarding the privacy and confidentiality of UAV-captured data. References: [6], [7]
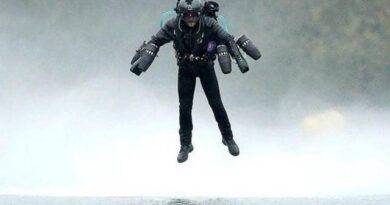
Counter-Drone Measures:
In recent years, there has been an increase in unauthorized drone activities, ranging from airspace violations to potential security threats. To counter these risks, organizations and authorities are developing counter-drone measures. These systems utilize advanced technologies such as radar, radio frequency detection, and signal jamming to detect and neutralize unauthorized UAVs. However, it is vital to ensure that these counter-drone measures do not interfere with legitimate UAV operations or compromise their cybersecurity. References: [8], [9]
As UAV operations continue to proliferate across industries, addressing the cybersecurity concerns associated with these autonomous aerial systems becomes paramount. By implementing robust security measures, including secure communication protocols, access controls, software updates, and data privacy safeguards, we can ensure the safe and secure operation of UAVs. Furthermore, ongoing research, collaboration among stakeholders, and regulatory frameworks will play a pivotal role in mitigating the evolving cybersecurity challenges in the realm of UAV operations, paving the way for a future where drones can be leveraged safely and effectively.
References:
[1] Johnson, D. W., & Potter, M. (2017). Cyber Security Analysis of Unmanned Aerial Systems. Proc. of the National Cyber Summit.
[2] Granjal, J., Monteiro, E., & Silva, J. S. (2015). Security in Internet of Things: From a Computer Science Perspective. IEEE Internet of Things Journal, 1(5), 394-403.
[3] Liu, X., Lao, L., & Jin, L. (2017). Cybersecurity in Unmanned Aerial Vehicles Systems: Risks, Vulnerabilities, and Countermeasures. IEEE Internet of Things Journal, 4(6), 2115-2124.
[4] Yan, R., Li, Z., Zhang, Y., Li, Z., Liu, Y., & Xiang, Y. (2020). Towards Secure and Reliable Unmanned Aerial Vehicle Networks: Opportunities and Challenges. IEEE Network, 34(1), 90-96. Further reading: https://ieeexplore.ieee.org/abstract/document/7470933/
[5] Tan, J., et al. (2020). Cybersecurity of Unmanned Aerial Systems: A Survey. IEEE Access, 8, 44047-44070.
[6] Nogueira, M., Arshad, M. R., Gomes, J., & Meneguette, R. I. (2020). Privacy and Data Protection in IoT-based Aerial Surveillance Systems: A Review. Computers & Electrical Engineering, 85, 106736.
[7] Ashraf, A., et al. (2018). Cyber Security for Unmanned Aerial Vehicle Systems. Journal of Information Security and Applications, 39, 99-118.
[8] Alenezi, A. O., & Alharbi, T. (2021). Drone Intrusion Detection System Using AI-Based Hybrid Techniques: A Review. IEEE Access, 9, 15775-15792.
[9] Cabezas, J., et al. (2018). Cybersecurity of Drones in Smart Cities. Procedia Computer Science, 138, 496-503.